Tài liệu Getters and Setters docx

Tài liệu Getters and Setters docx
... versatility of getters and setters, getting and setting property values
directly is considered bad coding practice. Set up and use getter and setter methods
instead.
Implicit get and set Methods ... setter methods
instead.
Implicit get and set Methods
Now that you understand the power and efficiency of using getter and setter methods, it's
time to introduce alte...

Tài liệu Java and XML docx
... missed her terribly,
and am anxious to return to spending time with her, my three basset hounds (Charlie, Molly, and
Daisy), and my labs (Seth and Moses).
And to my grandfather, Robert Earl ... APIs, and provides a standard interface for using the framework. More advanced frameworks
allow for processing of both static XML documents and XML generated by Java applications, and...

Tài liệu Speaking and Dictating docx
... the handwritten words into my
computer.
Writing by voice engages a different thought process than typing or
writing longhand. Like the transition from handwriting to typing, it took
effort and ... book! For
myself and for hundreds of thousands of other speech software users,
dictation now comes naturally—as much or more so than the unnatural,
but learned, skills of typing and handwritin...

Tài liệu Java and SOAP docx
... xsi:type="xsd:float">37</quantity>
Java and SOAP
1
Dedication
Once again, for my daughter Jessica.
Java and SOAP
34
Figure 3-1 shows the relationships between the three Worker Bees (Ben, Andrew, and
Lorraine), and the ... dimensions of the array are 3
by 2, and the figure shows the major dimension down and the minor dimension across.
Java and...

Tài liệu DNS and BIND docx
... Domain)
compiling and installing : B. Compiling and Installing BIND on a Sun
configuration file : (see boot file)
directives and resolvers (list) : F.1. BIND Name Server Boot File Statements
firewalls and ... Code
resources for : 3.1.1. Handy Mailing Lists and Usenet Newsgroups
running as non−root user : 10.11.4. Running BIND as a Non−Root User
statistics : 7.6.2. Understanding the...

Tài liệu Times and Tenses docx
... styles of clothes. They
put on new clothes and stand in front of cameras. Pictures
of models appear in newspapers and in magazines. People
see the pictures and want to buy the clothes. Fashion
models ... telephone, and
meets people. She uses a typewriter every day. She
puts papers away in the file cabinet. She stands
between her boss and his visitors. She helps her boss
to p...

Tài liệu Classification and Marking docx
... Systems, Inc. IP QoS Classification and Marking 2-13
© 2001, Cisco Systems, Inc. Classification and Marking -15
Monitoring and Troubleshooting
PBR
Monitoring and Troubleshooting
PBR
show route-map ...
where match commands are used to classify
packets and set commands are used to
process packets
• Route maps are applied to interfaces for
processing of inbound packets (forwardi...
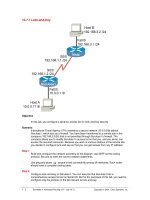
Tài liệu Lock-and-Key docx
...
The autocommand configuration is used to automate the process of creating a
temporary access list entry. Upon authentication, SanJose1 executes the access-
enable command and creates a temporary ...
10.0.0.11, you can test the lock -and- key configuration.
From Host B, Telnet to SanJose1’s Serial 0/0 (192.168.1.2). You are prompted to
authenticate with a username and password. En...
Từ khóa:
- tài liệu về switching and amplifying
- tài liệu thi ielts cho speaking and writing skill
- tài liệu bài tập lớn kỹ thuật xung số docx
- tài liệu family and friends 5 class book
- tai lieu family and friends 2
- Nghiên cứu sự hình thành lớp bảo vệ và khả năng chống ăn mòn của thép bền thời tiết trong điều kiện khí hậu nhiệt đới việt nam
- Nghiên cứu tổ chức pha chế, đánh giá chất lượng thuốc tiêm truyền trong điều kiện dã ngoại
- Một số giải pháp nâng cao chất lượng streaming thích ứng video trên nền giao thức HTTP
- Nghiên cứu tổ chức chạy tàu hàng cố định theo thời gian trên đường sắt việt nam
- đề thi thử THPTQG 2019 toán THPT chuyên thái bình lần 2 có lời giải
- Biện pháp quản lý hoạt động dạy hát xoan trong trường trung học cơ sở huyện lâm thao, phú thọ
- Giáo án Sinh học 11 bài 13: Thực hành phát hiện diệp lục và carôtenôit
- Giáo án Sinh học 11 bài 13: Thực hành phát hiện diệp lục và carôtenôit
- Quản lý hoạt động học tập của học sinh theo hướng phát triển kỹ năng học tập hợp tác tại các trường phổ thông dân tộc bán trú huyện ba chẽ, tỉnh quảng ninh
- Phối hợp giữa phòng văn hóa và thông tin với phòng giáo dục và đào tạo trong việc tuyên truyền, giáo dục, vận động xây dựng nông thôn mới huyện thanh thủy, tỉnh phú thọ
- Trả hồ sơ điều tra bổ sung đối với các tội xâm phạm sở hữu có tính chất chiếm đoạt theo pháp luật Tố tụng hình sự Việt Nam từ thực tiễn thành phố Hồ Chí Minh (Luận văn thạc sĩ)
- Phát hiện xâm nhập dựa trên thuật toán k means
- Nghiên cứu, xây dựng phần mềm smartscan và ứng dụng trong bảo vệ mạng máy tính chuyên dùng
- Nghiên cứu về mô hình thống kê học sâu và ứng dụng trong nhận dạng chữ viết tay hạn chế
- Nghiên cứu khả năng đo năng lượng điện bằng hệ thu thập dữ liệu 16 kênh DEWE 5000
- Định tội danh từ thực tiễn huyện Cần Giuộc, tỉnh Long An (Luận văn thạc sĩ)
- Tìm hiểu công cụ đánh giá hệ thống đảm bảo an toàn hệ thống thông tin
- BT Tieng anh 6 UNIT 2
- chuong 1 tong quan quan tri rui ro
- Giáo án Sinh học 11 bài 14: Thực hành phát hiện hô hấp ở thực vật
